Fortinet Single Sign-On
FSSO is a set of methods to transparently authenticate users to FortiGate and FortiCache devices. This means that the FortiAuthenticator unit is trusting the implicit authentication of a different system, and using that to identify the user. FortiAuthenticator takes this framework and enhances it with several authentication methods:
- Users can authenticate through a web portal and a set of embeddable widgets. l Users with FortiClient Endpoint Security installed can be automatically authenticated through the FortiClient SSO Mobility Agent.
- Users authenticating against Active Directory can be automatically authenticated. l RADIUS Accounting packets can be used to trigger an FSSO authentication. l Users can be identified through the FortiAuthenticator API. This is useful for integration with third party systems.
The FortiAuthenticator unit must be configured to collect the relevant user logon data. After this basic configuration is complete, the various methods of collecting the log in information can be set up as needed.
Domain controller polling
When the FortiAuthenticator runs for the first time, it will poll the domain controller (DC) logs backwards until either the end of the log file or the logon timeout setting, whichever is reached first.
When the FortiAuthenticator is rebooted, the memory cache is written to the disk, then re-read at startup, allowing the previous state to be retained. Windows DC polling restarts on boot, then searches backwards in the DC log files until it reaches either the log that matches the last known serial number found in the login cache file, the log that is older than the last recorded read time, or the end of the log file, whichever is reached first.
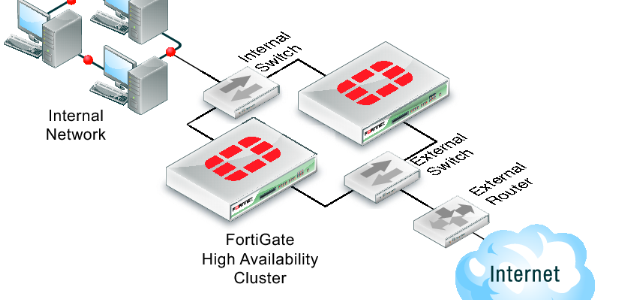
The currently logged in FSSO users list is cached in memory and periodically written to disk. In an active-passive HA cluster, this file is synchronized to the slave device.
Windows management instrumentation polling
The FortiAuthenticator supports Windows Management Instrumentation (WMI) polling to detect workstation log off. This validates the currently logged on user for an IP address that has been discovered by the DC polling detection method.
Remote WMI access requires that the related ports are opened in the Windows firewall, and access to a domain account that belongs to the Domain Admin group.
To open ports in the Windows firewall in Windows 7, run gpedit.msc, go to Computerconfiguration >
Administrative Templates > Network > Network Connections > Windows Firewall > Domain Profile, go to Allow remote admin exception, then enable remote admin exception and, if necessary, configure an IP subnet/range.
General settings
General settings
The FortiAuthenticator unit listens for requests from authentication clients and can poll Windows Active Directory servers.
To configure FortiAuthenticator FSSO polling:
- Go to Fortinet SSO Methods > SSO > General to open the Edit SSO Configuration The Edit SSO Configuration window contains sections for FortiGate, FSSO, and user group membership.
- In the FortiGate section, configure the following settings:
| Listening port |
Leave at 8000 unless your network requires you to change this. Ensure this port is allowed through the firewall. |
| Enable authentication |
Select to enable authentication, then enter a secret key, or password, in the Secret key field. |
| Login Expiry |
The length of time, in minutes, that users can remain logged in before the system logs them off automatically. The default is 480 minutes (8 hours). |
| Extend user session beyond logoff by |
The length of time, in seconds, that a user session is extended after the user logs off, from 0 (default) to 3600 seconds. |
| Enable NTLM
authentication |
Select to enable NTLM authentication, then enter the NETBIOS or DNS name of the domain that the login user belongs to in the Userdomain field. |
- In the Fortinet Single Sign-On (FSSO) section, configure the following settings:
| Maximum concurrent user sessions |
Enter the maximum number of concurrent FSSO login sessions a user is allowed to have. Use 0 for unlimited.
Select Configure Per User/Group to configure the maximum number of concurrent sessions for each user or group. See Fine-grained controls on page 112. |
| Log Level |
Select one of Debug, Info, Warning, or Error as the minimum severity level of events to log from the drop- down list.
Select Download all logs to download all FSSO logs to your management computer. |
General settings
| Enable Windows Active
Directory domain controller polling |
Select to enable Windows AD polling.
Select to enable polling additional logon events, including from devices using Kerberos authentication or from Mac OS X systems, and from event IDs 672, 680, 4776, and 4768. |
| Enable polling additional logon events |
When additional active directory logon event IDs is enabled, event IDs 528, 540, and 4624 are also polled. These event are generated when a user attempts to access a domain service or resource. When a user logs off from the workstation, such an event will be generated.
Enter the additional logon event timeout time in the Additional logon event timeout field, from 1 to 480 minutes, with 5 minutes being the default time.
Note: After a user logs off, their SSO session will stay active for the above configured period of time. During this time, if another user changes to the previous user’s IP address, they may be able to bypass the necessary authentication. For this reason, it is strongly recommended that the timeout time be kept short. |
| Enable DNS
lookup to get IP
from workstation name |
Select to use DNS lookup to get IP address information when an event contains only the workstation name.
This option is enabled by default. |
| Directly use domain DNS
suffix in lookup |
Select to use the domain DNS suffix when doing a DNS lookup.
This option is disabled by default. |
| Enable reverse DNS lookup to get workstation name from IP |
Select to enable reverse DNS lookup. Reverse DNS lookup is used when an event contains only an IP address and no workstation name.
This option is enabled by default. |
| Do one more DNS lookup to get full list of IPs after reverse lookup of workstation name |
Reverse DNS lookup is used when an event contains only an IP address and no workstation name. Once the workstation name is determined, it is used in the DNS lookup again to get more complete IP address
information. This is useful in environments where workstations have multiple network interfaces.
This option is disabled by default. |
| Include account name ending
with $ (usually computer account) |
Accounts that end in “$” used to exclusively denote computer accounts with
no actual user, but in some cases, valid accounts imported from dated systems can feature them.
This option is disabled by default. |
| Enable Radius Accounting SSO clients |
Select to enable the detection of users sign-ons and sign- offs from incoming RADIUS accounting (Start, Stop, and Interim-Update) records. |
| Use RADIUS realm as
Windows Active
Directory domain |
Select to use the RADIUS realm as the Windows AD domain. |
| Enable Syslog SSO |
Select to enable Syslog SSO. |
General settings
| Enable FortiClient SSO
Mobility Agent Service |
Select to enable single sign-on (SSO) by clients running FortiClient Endpoint Security. For more information, see FortiClient SSO Mobility Agent on page 123. |
| FortiClient listening port |
Enter the FortiClient listening port number. |
| Enable authentication |
Select to enable authentication, then enter a secret key, or password, in the Secret key field. |
| Keep-alive interval |
Enter the duration between keep-alive transmissions, from 1 to 60 minutes. Default is 5 minutes. |
| Idle timeout |
Enter an amount of time after which to logoff a user if their status is not updated. The value cannot be lower than the Keep-alive interval value. |
| Enable NTLM |
Select to enable the NT LAN Manager (NTLM) to allow logon of users who are connected to a domain that does not have the FSSO DC Agent installed. Disable NTLM authentication only if your network does not support NTLM authentication for security or other reasons. Enter an amount of time after which NTLM authentication expires in the NTLM authentication expiry field, from 1 to 10080 minutes (7 days). |
| Enable hierarchical FSSO tiering |
Select to enable hierarchical FSSO tiering. Enter the collector listening port in the Collectorlistening port field. |
| Enable DC/TS Agent Clients |
Select to enable clients using DC or TS Agent. Enter the UDP port in the
DC/TS Agent listening port field. Default is 8002.
Select Enable authentication to enable authentication, then enter a secret key, or password, in the Secret key field. |
| Restrict auto- discovered domain controllers to configured domain
controllers |
Select to enable restricting automatically discovered domain controllers to already configured domain controllers only. See Domain controllers on page 114. |
| Enable Windows Active
Directory workstation IP
verification |
Select to enable workstation IP verification with Windows Active Directory. If enabled, select Enable IP change detection via DNS lookup to detect IP changes via DNS lookup. |
- In the UserGroup Membership section, configure the following settings:
General settings
| Group cache mode |
Select the group cache mode:
l Passive: Items have an expiry time after which the are removed and re-queried on the next logon.
l Active: Items are periodically updated for all currently logged on users. |
| Group cache item
lifetime |
Enter the amount of time after which items will expire (default = 480 minutes). This is only available when the group cache mode is set to Passive. |
| Do not use cached groups… |
Select to prevent using cached groups and to always load groups from server for the following SSO sources: l Windows Active Directory domain controller polling l RADIUS Accounting SSO l Syslog SSO
l FortiClient SSO Mobility Agent l DC Agent l TS Agent
l User login portal l SSO web service |
| Base distinguished names to search… |
Enter the base distinguished names to search for nesting of users or groups into cross domain and domain local groups. |
- Select OK to apply the settings.