FortiGate dialup-client configurations
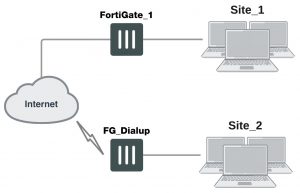
This section explains how to set up a FortiGate dialup-client IPsec VPN. In a FortiGate dialup-client configuration, a FortiGate unit with a static IP address acts as a dialup server and a FortiGate unit having a dynamic IP address initiates a VPN tunnel with the FortiGate dialup server.
- The following topics are included in this section: Configuration overview
- FortiGate dialup-client configuration steps
- Configure the server to accept FortiGate dialup-client connections
- Configure the FortiGate dialup client
Configuration overview
A dialup client can be a FortiGate unit. The FortiGate dialup client typically obtains a dynamic IP address from an ISP through the Dynamic Host Configuration Protocol (DHCP) or Point-to-Point Protocol over Ethernet (PPPoE) before initiating a connection to a FortiGate dialup server.
Example FortiGate dialup-client configuration
In a dialup-client configuration, the FortiGate dialup server does not rely on a Phase 1 remote gateway address to establish an IPsec VPN connection with dialup clients. As long as authentication is successful and the IPsec security policy associated with the tunnel permits access, the tunnel is established.
Several different ways to authenticate dialup clients and restrict access to private networks based on client credentials are available. To authenticate FortiGate dialup clients and help to distinguish them from FortiClient dialup clients when multiple clients will be connecting to the VPN through the same tunnel, best practices dictate that you assign a unique identifier (local ID or peer ID) to each FortiGate dialup client. For more information, see Phase 1 parameters on page 1624.
Whenever you add a unique identifier (local ID) to a FortiGate dialup client for iden- tification purposes, you must select Aggressive mode on the FortiGate dialup server and also specify the identifier as a peer ID on the FortiGate dialup server. For more information, see Phase 1 parameters on page 1624.
Users behind the FortiGate dialup server cannot initiate the tunnel because the FortiGate dialup client does not have a static IP address. After the tunnel is initiated by users behind the FortiGate dialup client, traffic from the private network behind the FortiGate dialup server can be sent to the private network behind the FortiGate dialup client.
Encrypted packets from the FortiGate dialup client are addressed to the public interface of the dialup server. Encrypted packets from the dialup server are addressed either to the public IP address of the FortiGate dialup client (if the dialup client connects to the Internet directly), or if the FortiGate dialup client is behind a NAT device, encrypted packets from the dialup server are addressed to the public IP address of the NAT device.
If a router with NAT capabilities is in front of the FortiGate dialup client, the router must be NAT-T compatible for encrypted traffic to pass through the NAT device. For more information, see Phase 1 parameters on page 1624.
When the FortiGate dialup server decrypts a packet from the FortiGate dialup client, the source address in the IP header may be one of the following values, depending on the configuration of the network at the far end of the tunnel:
- If the FortiGate dialup client connects to the Internet directly, the source address will be the private IP address of a host or server on the network behind the FortiGate dialup client.
- If the FortiGate dialup client is behind a NAT device, the source address will be the public IP address of the NAT device.
In some cases, computers on the private network behind the FortiGate dialup client may (by co-incidence) have IP addresses that are already used by computers on the network behind the FortiGate dialup server. In this type of situation (ambiguous routing), conflicts may occur in one or both of the FortiGate routing tables and traffic destined for the remote network through the tunnel may not be sent.
In many cases, computers on the private network behind the FortiGate dialup client will most likely obtain IP addresses from a local DHCP server behind the FortiGate dialup client. However, unless the local and remote networks use different private network address spaces, unintended ambiguous routing and IP-address overlap issues may arise.
To avoid these issues, you can configure FortiGate DHCP relay on the dialup client instead of using a DHCP server on the network behind the dialup client. The FortiGate dialup client can be configured to relay DHCP requests from the local private network to a DHCP server that resides on the network behind the FortiGate dialup server. You configure the FortiGate dialup client to pass traffic from the local private network to the remote network by enabling FortiGate DHCP relay on the FortiGate dialup client interface that is connected to the local private network.
Afterward, when a computer on the network behind the dialup client broadcasts a DHCP request, the dialup client relays the message through the tunnel to the remote DHCP server. The remote DHCP server responds with a private IP address for the computer. To avoid ambiguous routing and network overlap issues, the IP addresses assigned to computers behind the dialup client cannot match the network address space used by the private network behind the FortiGate dialup server.
Preventing network overlap in a FortiGate dialup-client configuration
When the DHCP server resides on the private network behind the FortiGate dialup server, the IP destination address specified in the IPsec security policy on the FortiGate dialup client must refer to that network.
You must add a static route to the DHCP server FortiGate unit if it is not directly con- nected to the private network behind the FortiGate dialup server; its IP address does not match the IP address of the private network. Also, the destination address in the IPsec security policy on the FortiGate dialup client must refer to the DHCP server address. The DHCP server must be configured to assign a range of IP addresses dif- ferent from the DHCP server’s local network, and also different from the private net- work addresses behind the FortiGate dialup server. See Dynamic DNS configuration on page 1688.
FortiGate dialup-client infrastructure requirements
The requirements are:
- The FortiGate dialup server must have a static public IP address.
- NAT mode is required if you want to create a route-based VPN.
- The FortiGate dialup server may operate in either NAT mode or transparent mode to support a policy-based VPN.
- Computers on the private network behind the FortiGate dialup client can obtain IP addresses either from a DHCP server behind the FortiGate dialup client, or a DHCP server behind the FortiGate dialup server.
- If the DHCP server resides on the network behind the dialup client, the DHCP server must be configured to assign IP addresses that do not match the private network behind the FortiGate dialup server.
- If the DHCP server resides on the network behind the FortiGate dialup server, the DHCP server must be configured to assign IP addresses that do not match the private network behind the FortiGate dialup client.
FortiGate dialup-client configuration steps
The procedures in this section assume that computers on the private network behind the FortiGate dialup client obtain IP addresses from a local DHCP server. The assigned IP addresses do not match the private network behind the FortiGate dialup server.
In situations where IP-address overlap between the local and remote private networks is likely to occur, FortiGate DHCP relay can be configured on the FortiGate dialup cli- ent to relay DHCP requests to a DHCP server behind the FortiGate dialup server. For more information, see FortiClient dialup-client configurations on page 1702.
Configuring dialup client capability for FortiGate dialup clients involves the following general configuration steps:
- Determine which IP addresses to assign to the private network behind the FortiGate dialup client, and add the IP addresses to the DHCP server behind the FortiGate dialup client. Refer to the software supplier’s documentation to configure the DHCP server.
- Configure the FortiGate dialup server. See FortiGate dialup-client configuration steps on page 1718.
- Configure the FortiGate dialup client. See FortiGate dialup-client configuration steps on page 1718.
Configure the server to accept FortiGate dialup-client connections
Before you begin, optionally reserve a unique identifier (peer ID) for the FortiGate dialup client. The dialup client will supply this value to the FortiGate dialup server for authentication purposes during the IPsec Phase 1 exchange. In addition, the value will enable you to distinguish FortiGate dialup-client connections from FortiClient dialup-client connections. The same value must be specified on the dialup server and on the dialup client.
1. At the FortiGate dialup server, define the Phase 1 parameters needed to authenticate the FortiGate dialup client and establish a secure connection. See Phase 1 parameters on page 1624. Enter these settings in particular:
Name Enter a name to identify the VPN tunnel. This name appears in Phase 2 configurations, security policies and the VPN monitor.
Remote Gateway Select Dialup User.
Local Interface Select the interface through which clients connect to the FortiGate unit.
Mode If you will be assigning an ID to the FortiGate dialup client, select Aggress– ive.
Peer Options If you will be assigning an ID to the FortiGate dialup client, select This
peer ID and type the identifier that you reserved for the FortiGate dialup cli- ent into the adjacent field.
2. Define the Phase 2 parameters needed to create a VPN tunnel with the FortiGate dialup client. See Phase 2 parameters on page 1642. Enter these settings in particular:
Name Enter a name to identify this Phase 2 configuration.
Phase 1 Select the name of the Phase 1 configuration that you defined.
3. Define names for the addresses or address ranges of the private networks that the VPN links. See Defining VPN
security policies on page 1648. Enter these settings in particular:
- Define an address name for the server, host, or network behind the FortiGate dialup server.
- Define an address name for the private network behind the FortiGate dialup client.
4. Define the security policies to permit communications between the private networks through the VPN tunnel.
Route-based and policy-based VPNs require different security policies. For detailed information about creating security policies, see Defining VPN security policies on page 1648.
Route–based VPN security policy
Define an ACCEPT security policy to permit communications between hosts on the private network behind the FortiGate dialup client and the private network behind this FortiGate dialup server. Because communication cannot be initiated in the opposite direction, there is only one policy.
1. Go to Policy & Objects > IPv4 Policy and select Create New.
2. Leave the Policy Type as Firewall and leave the Policy Subtype as Address.
3. Enter these settings in particular:
Incoming Interface Select the VPN tunnel (IPsec interface) created in Step 1.
Source Address Select All.
Outgoing Interface Select the interface that connects to the private network behind this FortiGate unit.
Destination Address Select All.
Action Select ACCEPT.
Enable NAT Disable
Policy–based VPN security policy
1. Go to Policy & Objects > IPv4 Policy and select Create New.
2. Enter these settings in particular:
Incoming Interface Select the interface that connects to the private network behind this FortiGate unit.
Source Address Select the address name that you defined for the private network behind this FortiGate unit.
Outgoing Interface Select the FortiGate unit’s public interface.
Destination Address Select the address name that you defined.
VPN Tunnel Select Use Existing and select the name of the Phase 1 configuration that you created in Step1. from the drop-down list.
Select Allow traffic to be initiated from the remote site to enable traffic from the remote network to initiate the tunnel.
Clear Allow outbound to prevent traffic from the local network from ini- tiating the tunnel after the tunnel has been established.
3. To prevent traffic from the local network from initiating the tunnel after the tunnel has been established, you need to disable the outbound VPN traffic in the CLI
config firewall policy edit <policy_number>
set outbound disable
end
Place the policy in the policy list above any other policies having similar source and destination addresses. If configuring a route-based policy, configure a default route for VPN traffic on this interface.
Configure the FortiGate dialup client
Configure the FortiGate dialup client.
1. At the FortiGate dialup client, define the Phase 1 parameters needed to authenticate the dialup server and establish a secure connection. See Phase 1 parameters on page 1624. Enter these settings in particular:
Name Enter a name to identify the VPN tunnel.
Remote Gateway Select Static IP Address.
IP Address Type the IP address of the dialup server’s public interface.
Local Interface Select the interface that connects to the public network.
Mode The FortiGate dialup client has a dynamic IP address, select Aggressive.
Advanced Select to view the following options.
Local ID If you defined a peer ID for the dialup client in the FortiGate dialup server configuration, enter the identifier of the dialup client. The value must be identical to the peer ID that you specified previously in the FortiGate dialup server configuration.
2. Define the Phase 2 parameters needed to create a VPN tunnel with the dialup server. See Phase 2 parameters on page 1642. Enter these settings in particular:
Name Enter a name to identify this Phase 2 configuration.
Phase 1 Select the name of the Phase 1 configuration that you defined.
3. Define names for the addresses or address ranges of the private networks that the VPN links. See Defining VPN security policies on page 1648. Enter these settings in particular:
- Define an address name for the server, host, or network behind the FortiGate dialup server.
- Define an address name for the private network behind the FortiGate dialup client.
4. Define security policies to permit communication between the private networks through the VPN tunnel. Route- based and policy-based VPNs require different security policies. For detailed information about creating security policies, see Defining VPN security policies on page 1648.
Route–based VPN security policy
Define an ACCEPT security policy to permit communications between hosts on the private network behind this FortiGate dialup client and the private network behind the FortiGate dialup server. Because communication cannot be initiated in the opposite direction, there is only one policy.
1. Go to Policy & Objects > IPv4 Policy and select Create New.
2. Leave the Policy Type of Firewall and leave the Policy Subtype as Address.
3. Enter these settings in particular:
Incoming Interface Select the interface that connects to the private network behind this FortiGate unit.
Source Address Select All.
Outgoing Interface Select the VPN tunnel (IPsec interface) created in Step 1.
Destination Address Select All.
Action Select ACCEPT.
Enable NAT Disable
Policy–based VPN security policy
Define an IPsec security policy to permit communications between the source and destination addresses.
1. Go to Policy & Objects > IPv4 Policy and select Create New.
2. Enter these settings in particular:
Incoming Interface Select the interface that connects to the private network behind this FortiGate unit.
Source Address Select the address name that you defined for the private network behind this FortiGate unit.
Outgoing Interface Select the FortiGate unit’s public interface.
Destination Address Select the address name that you defined for the private network behind the dialup server.
VPN Tunnel Select Use Existing and select the name of the Phase 1 configuration that you created in Step 1 from the drop-down list.
Clear Allow traffic to be initiated from the remote site to prevent traffic from the remote network from initiating the tunnel after the tunnel has been established.
Place the policy in the policy list above any other policies having similar source and destination addresses.