Chapter 22 – Security Profiles
This FortiOS Handbook chapter contains the following sections:
- What’s new in FortiOS 5.4 lists and describes the new security profile features in FortiOS 5.4.
- Security Profiles overview describes Security Profiles components and their relation to firewall policies, as well as SSL content scanning and inspection. We recommend starting with this section to become familiar with the different features in your FortiGate unit.
- AntiVirus explains how the FortiGate unit scans files for viruses and describes how to configure the antivirus options.
- Web filter describes basic web filtering concepts, FortiGuard Web Filtering, the order in which the FortiGate unit performs web filtering, and configuration.
- Application Control describes how your FortiGate unit can detect and take action against network traffic based on the application generating the traffic.
- FortiClient Profiles describes the FortiClient Profiles endpoint protection features and configuration.
- Intrusion protection explains basic Intrusion Protection System (IPS) concepts and how to configure IPS options;
- includes guidance and a detailed table for creating custom signatures as well as several examples.
- Custom Application & IPS Signatures describes how to create custom Application Control and IPS signatures. Anti-Spam filter explains how the FortiGate unit filters email, describes how to configure the filtering options and the action to take with email detected as spam.
- Data leak prevention describes the DLP features that allow you to prevent sensitive data from leaving your network and explains how to configure the DLP rules, compound rules, and sensors.
- ICAP support describes how to off load traffic to a separate server specifically set up for the specialized processing of the traffic.
- Other Security Profiles considerations describes topics like Security Profiles VDOMs, conserve mode, SSL content scanning and inspection, Using wildcards and Perl regular expressions, Adding External Security Devices, CPU allocation and tuning commands to survive reboot and so on.
What‘s new in FortiOS 5.4
Proxy and flow-based inspection per VDOM
You can select flow or proxy mode from the System Information dashboard widget to control your FortiGate’s security profile inspection mode. Having control over flow and proxy mode is helpful if you want to be sure that only flow inspection mode is used (and that proxy inspection mode is not used). As well, switching to flow inspection mode also turns off the explicit web proxy and the explicit FTP proxy, making sure that no proxying can occur.
In most cases proxy mode (the default) is preferred because more security profile features are available and more configuration options for these individual features are available. Some implementations; however, may require all security profile scanning to only use flow mode. In this case, you can set your FortiGate to flow mode knowing that proxy mode inspection will not be used.
If you select flow-based to use external servers for FortiWeb and FortiMail you must use the CLI to set a Web Application Firewall profile or Anti-Spam profile to external mode and add the Web Application Firewall profile or Anti-Spam profile to a firewall policy.
Changing between proxy and flow mode
By default proxy mode is enabled and you change to flow mode by changing the Inspection Mode on the System Information dashboard widget. When you select Flow–based you are reminded that all proxy mode profiles are converted to flow mode, removing any proxy settings. As well proxy-mode only features (for example, Web Application Profile) are removed from the GUI.
In addition, when you select Flow–based the Explicit Web Proxy and Explicit FTP Proxy features are removed from the GUI and the CLI. This includes Explicit Proxy firewall policies.
If required you can change back to proxy mode just as easily. As well, if your FortiGate has multiple VDOMs you can set the inspection mode independently for each VDOM.
Security profile features available in proxy mode
When set to proxy mode, the following security profiles are available:
- AntiVirus
- Web Filter
- DNS Filter
- Application Control
- Intrusion Protection
- Anti-Spam
- Data Leak Prevention
- VoIP
- ICAP
- Web Application Firewall
- FortiClient Profiles
- Proxy Options
- SSL Inspection
- Web Rating Overrides
- Web Profile Overrides
- ICAP Servers
In proxy mode, from the GUI you can only configure antivirus and web filter security profiles in proxy mode. From the CLI you can configure flow-based antivirus profiles, web filter profiles and DLP profiles and they will appear on the GUI and include their inspection mode setting. Also, flow-based profiles created when in flow mode are still available when you switch to proxy mode.
Security profile features available in flow mode
When you change to flow mode, proxy mode antivirus and web filter security profiles are converted to flow mode and the following reduced set of security profiles features are available:
- AntiVirus
- Web Filter
- Application Control
- Cloud Access Security Inspection
- Intrusion Protection
- FortiClient Profiles
- SSL Inspection
- Web Rating Overrides
In flow mode, antivirus and web filter profiles only include flow-mode features. Web filtering and virus scanning is still done with the same engines and to the same accuracy, but some inspection options are limited or not available in flow mode. Application control, intrusion protection, and FortiClient profiles are not affected when switching between flow and proxy mode.
Unfortunately CASI does not work when using Proxy-based profiles for AV or Web fil- tering. Make sure to only use Flow-based profiles in combination with CASI on a specific policy.
Even though VoIP profiles are not available from the GUI in flow mode, the FortiGate can process VoIP traffic. In this case the appropriate session helper is used (for example, the SIP session helper).
Setting flow or proxy mode doesn’t change the settings available from the CLI. However, you can’t save security profiles that are set to proxy mode.
You can also add add proxy-only security profiles to firewall policies from the CLI. So, for example, you can add a VoIP profile to a security policy that accepts VoIP traffic. This practice isn’t recommended because the setting will not be visible from the GUI.
Proxy mode and flow mode antivirus and web filter profile options
The following tables list the antivirus and web filter profile options available in proxy and flow modes.
|
Antivirus features in proxy and flow mode |
||
| Feature | Proxy | Flow |
|
Scan Mode (Quick or Full) |
no |
yes |
|
Detect viruses (Block or Monitor) |
yes |
yes |
|
Inspected protocols |
yes |
no (all relevant protocols are inspected) |
|
Inspection Options |
yes |
yes (not available for quick scan mode) |
|
Treat Windows Executables in Email Attachments as Viruses |
yes |
yes |
|
Include Mobile Malware Protection |
yes |
yes |
Web Filter features in proxy and flow mode
Feature Proxy Flow
FortiGuard category based filter yes yes (show, allow, monitor, block)
Category Usage Quota yes no
Allow users to override blocked categories (on some models) yes no
Search Engines yes no
Enforce ‘Safe Search’ on Google, Yahoo!, Bing, Yandex yes no
YouTube Education Filter yes no
Log all search keywords yes no
Static URL Filter yes yes
Block invalid URLs yes no
URL Filter yes yes
Block malicious URLs discovered by FortiSand- box yes yes
Web Content Filter yes yes
| Feature Proxy Flow | |
|
Rating Options yes yes |
|
|
Allow websites when a rating error occurs yes yes |
|
|
Rate URLs by domain and IP Address yes yes |
|
|
Block HTTP redirects by rating yes no |
|
|
Rate images by URL yes no |
|
|
Proxy Options yes no |
|
|
Restrict Google account usage to specific yes no domains |
|
|
Provide details for blocked HTTP 4xx and 5xx yes no errors |
|
|
HTTP POST Action yes no |
|
|
Remove Java Applets Remove ActiveX yes no |
|
|
Remove Cookies yes no |
|
|
Filter Per-User Black/White List yes no |
|
Cloud Access Security Inspection (CASI)
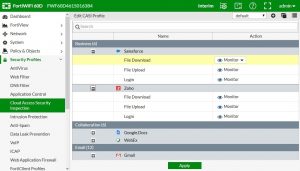
This feature introduces a new security profile called Cloud Access Security Inspection (CASI) that provides support for fine-grained control on popular cloud applications, such as YouTube, Dropbox, Baidu, and Amazon. The CASI profile is applied on a policy much like any other security profile.
Unfortunately CASI does not work when using Proxy-based profiles for AV or Web fil- tering for example.
Make sure to only use Flow-based profiles in combination with CASI on a specific policy.
For this feature, Deep Inspection of Cloud Applications (set deep-app-inspection [enable| disable]) has been moved out of the Application Control security profile options.
You will find the Cloud Access Security Inspection feature under Security Profiles > Cloud Access Security Inspection, but you must first enable it in the Feature store under System > Feature Select > CASI.
Editing CASI profiles
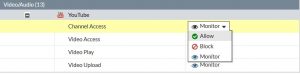
The CASI profile application list consists of the Application Name, Category, and Action. A default CASI profile exists, with the option to create custom profiles. For each CASI profile application, the user has the option to Allow, Block, or Monitor the selected cloud application. The following image demonstrates the ability to Allow, Block, or Monitor YouTube using CASI:
When the user drills down into a selected cloud application, the following options are available (depending on the type of service):
- For business services, such as Salesforce and Zoho: Option to allow, block, or monitor file download/upload and login.
- For collaboration services, such as Google.Docs and Webex: Option to allow, block, or monitor file access/download/upload and login.
- For web email services, such as Gmail and Outlook: Option to allow, block, or monitor attachment download/upload, chat, read/send message.
- For general interst services, such as Amazon, Google, and Bing: Option to allow, block, or monitor login, search phase, and file download/upload.
- For social media services, such as Facebook, Twitter, and Instagram: Option to allow, block, or monitor chat, file download/upload, post, login.
- For storage backup services, such as Dropbox, iCloud, and Amazon Cloud Drive: Option to allow, block, or monitor file access/download/upload and login.
- For video/audio services, such as YouTube, Netflix, and Hulu: Option to allow, block, or monitor channel access, video access/play/upload, and login.
CLI Syntax
configure application casi profile edit “profile name”
set comment “comment”
set replacemsg-group “xxxx”
set app-replacemsg [enable|disable]
configure entries edit
set application “app name” set action [block|pass]
set log [enable|disable]
next edit 2
next end
configure firewall policy edit “1”
set casi-profile “profile name” next
end
config firewall sniffer edit 1
set casi-profile-status [enable|disable]
set casi-profile “sniffer-profile” next
end
config firewall interface-policy edit 1
set casi-profile-status [enable|disable]
set casi-profile “2” next
end
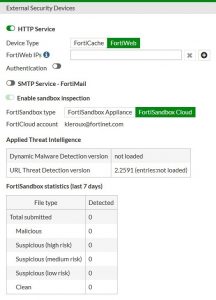
External Security Devices
External Security Devices can be configured as means to offload processes to other devices, such as a FortiWeb, FortiCache, or FortiMail. Example processes could include HTTP inspection, web caching, and anti-spam.
To configure such a device, go to System > External Security Devices.
FortiWeb
To be able to offload HTTP inspection to a FortiWeb device you should:
1. Go to System > External Security Devices, enable HTTP Service, select FortiWeb and add the IP address of your FortiCache device.
2. Go to Policy & Objects > IPv4 Policy, add or edit a firewall policy and select Web Application Firewall. When you add Web Application Firewall to a firewall policy, web traffic accepted by the policy is offloaded to the FortiWeb device for processing.
Enabling FortiWeb on the External Security Devices page adds the following configuration to the CLI:
config system wccp set service-id 51
set router-id 5.5.5.5 (the IP address of the FortiGate interface that communicates with the FortiWeb)
set group address 0.0.0.0
set server-list 5.5.5.25 255.255.255.255 (the IP address of the FortiWeb)
set authentication disable set forward-method GRE
set return-method GRE
set assignment-method HASH
end
FortiCache
To be able to offload Web Caching to a FortiCache device you should:
1. Go to System > External Security Devices, enable HTTP Service, select FortiCache and add the IP address of your FortiCache device.
2. Go to Policy & Objects > IPv4 Policy, add or edit a firewall policy and select Web Cache.
When you add web caching to a firewall policy, web traffic accepted by the policy is offloaded to the FortiCache device for processing.
Enabling FortiCache on the External Security Devices page adds the following configuration to the CLI:
config system wccp set service-id 51
set router-id 5.5.5.5 (the IP address of the FortiGate interface that communicates with the FortiCache)
set group address 0.0.0.0
set server-list 5.5.5.45 255.255.255.255 (the IP address of the FortiCache)
set authentication disable set forward-method GRE
set return-method GRE
set assignment-method HASH
end
FortiMail
To be able to offload Anti-Spam processing to a FortiMail device you should:
1. Go to System > Feature Select and turn on Anti–Spam Filter.
2. Go to System > External Security Devices, enable SMTP Service – FortiMail and add the IP address of your FortiMail device.
3. Go to Security Profiles > Anti-Spam and edit an Anti-Spam profile and set Inspection Device to External.
4. Go to Policy & Objects > IPv4 Policy, add or edit a Firewall policy, enable Anti–Spam and select the profile for which you set Inspection Device to External.
When you add this Anti-Spam profile to a firewall policy, email traffic accepted by the policy is offloaded to the FortiMail device for processing.
If your FortiGate or VDOM inspection mode is set to flow-based you must use the CLI to set an Anti-Spam profile to external mode and add the Anti-Spam profile to a fire- wall policy.
Enabling FortiMail on the External Security Devices page adds the following configuration to the CLI:
config system wccp set service-id 52
set router-id 5.5.5.5 (the IP address of the FortiGate interface that communicates with the FortiMail)
set group address 0.0.0.0
set server-list 5.5.5.65 255.255.255.255 (the IP address of the FortiMail)
set authentication disable set forward-method GRE
set return-method GRE
set assignment-method HASH
end
Selecting External in the Anti-Spam profile adds the following configuration to the CLI:
config spamfilter profile edit default
set external enable end
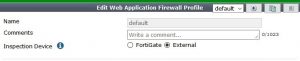
Web Application Firewall
Go to Security Profiles > Web Application Firewall. From here you can customize the default Web Application Firewall profile, or create new profiles, to protect against a variety of web-based threats. Web Application Firewall profiles can be created with a variety of options (Signatures and Constraints), similar to other security profiles.
You can set the Web Application Firewall to use an External Security Device, such as FortiWeb, by setting Inspection Device to External.
Configure the ability to store FortiClient configuration files (171380)
1. Enable the advanced FortiClient configuration option in the endpoint profile:
config endpoint-control profile edit “default”
set forticlient-config-deployment enable set fct-advanced-cfg enable
set fct-advanced-cfg-buffer “hello” set forticlient-license-timeout 1 set netscan-discover-hosts enable
next end
2. Export the configuration from FortiClient (xml format).
3. Copy the contents of the configuration file and try to paste in the advanced FortiClient configuration box.
If the configuration file is greater than 32k, you need to use the following CLI:
config endpoint-control profile edit <profile>
config forticlient-winmac-settings config extra-buffer-entries
edit <entry_id>
set buffer xxxxxx next
end
next end
FortiOS 5.4 no longer supports FortiClient 5.0 or earlier (289455)
FortiOS 5.2 would support FortiClient 5.0 (only if the FortiGate upgraded to FortiOS 5.2), however FortiOS 5.4 will no longer support FortiClient 5.0. Customers need to purchase a FortiClient 5.4 subscription-based FortiClient license.
Session timers for IPS sessions (174696 163930)
The standard FortiOS session-ttl (time to live) timer for IPS sessions has been introduced to reduce synchronization problems between the FortiOS Kernel and IPS. This has been added so that FortiGate hard- coded timeout values can be customized, and IPS was using too much overall memory.
Botnet protection with DNS Filter (293259)
The new botnet list from FortiGuard can be used to block DNS requests to known botnet C&C IP addresses within a new DNS filter profile.
You can view the botnet list by going to System > FortiGuard > Botnet Definitions.
Secure white list database (288365)
Secure white list exemption for SSL deep inspection. To enable, go to Security Profiles > SSL/SSH Inspection and enable Exempt from SSL Inspection and enable Reputable Websites.
Mobile Malware Definition update (288022)
Mobile Malware is a separate license and can be downloaded as a separate object. It is packaged with the same FortiGuard object as the client app signatures. These signatures can be enabled in AV profiles by selecting Include Mobile Malware Protection.
Options not supported by the new quick mode flow-based virus scanning (288317)
Files cannot be sent to FortiSandbox for inspection while in quick mode flow-based virus scanning, and so the GUI option for it has been removed. No option to switch between quick mode and full mode, as choice between Proxy and Flow based inspection has been removed.
Add mobile malware to FortiGuard licenses page and include more version information (290049)
An entry and version information for Mobile Malware Definitions has been added in the License Information table under System > FortiGuard. Also, main items have been bolded and sub-items have been indented for clarification.
Secure white-list DB for flow based UTM features (287343)
A new feature that gathers a list of reputable domain names that can be excluded from SSL deep inspection. This list is periodically updated and downloaded to FortiGate units through FortiGuard.
Syntax:
config firewall ssl-ssh-profile edit deep-inspection
set whitelist enable
end
New customizable replacement message that appears when an IPS sensor blocks traffic (240081)
A new replacement message will appear specifically for IPS sensor blocked Internet access, to differentiate between IPS sensor blocking and application control blocking.
Low end models don’t support flow AV quick mode and don’t support the IPS block-malicious- url option (288318)
AV quick mode and the IPS block-malicious-url option have been disabled on low-end FortiGate models, however these features can be enabled if the FortiGate unit has a hard disk. Low-end models will only supportFullscan mode (the option is left in the GUI to show which mode is active for the user).
New quick mode flow-based virus scanning (281291)
When configuring flow-based virus scanning you can now choose between quick and full mode. Full mode is the same as flow-based scanning in FortiOS 5.2. Quick mode uses a compact antivirus database and advanced techniques to improve performance. Use the following command to enable quick mode in an antivirus profile:
config antivirus profile edit <profile-name>
set scan-mode {quick | full}
end
CVE–IDs now appear in the FortiOS IPS signature list (272251)
The signature list can be found at Security Profiles > Intrusion Protection > View IPS Signatures.
Mobile malware protection added to Antivirus configuration (288022)
FortiGuard can now download signatures to enhance mobile antivirus protection.
To enable this option, go to Security Profiles > AntiVirus and enable Include Mobile Malware Protection.
Botnet protection added (254959)
The latest Botnet database is available from FortiGuard. You can see the version of the database and display its contents from the System > FortiGuard GUI page. You can also block, monitor or allow outgoing connections to Botnet sites for each FortiGate interface.
FortiSandbox URL database added
You can see the version of the database and display its contents from the System > FortiSandbox GUI page.
New Web Filter profile whitelist setting and changes to blacklist setting (283855, 285216)
Domain reputation can now be determined by “common sense”, for sites such as Google, Apple, and even sites that may contain sensitive material that would otherwise be trusted (i.e. there is no risk of receiving botnets or malicious attacks). You can tag URL groups with flags that exempt them from further sandboxing or AV analyzing.
You can identify reputable sites and enable certain bypasses under Security Profiles > Web Filter. Similarly, you can exempt the identified reputable sites from SSL inspection.
CLI Syntax
config firewall ssl-ssh-profile edit <profile-name>
set whitelist [enable | disable]
end
config webfilter profile edit <profile-name>
config web
set whitelist exempt-av exempt-webcontent exempt-activex-java-cookie exempt-dlp exempt-rangeblock extended-log-others
end
end
Support security profile scanning of RPC over HTTP traffic (287508)
This protocol is used by Microsoft Exchange Server so this feature supports security profile features such as virus scanning of Microsoft Exchange Server email that uses RPC over HTTP.
Users now allowed to override blocked categories using simple, wildcard, and regex expres- sions to identify the URLs that are blocked (270165)
This feature is also called per-user BWL. To be able to configure this feature from the GUI enter the following command:
config system global
set per-user-bwl enable end
Then go to Security Profiles > Web Filtering, edit a web filtering profile and select Allow users to override blocked categories.
Use the following command to configure this feature from the CLI:
config webfilter profile edit <profile-name>
set options per-user-bwl end
Set flow or proxy mode for your FortiGate (or per VDOM) (266028)
You can configure your FortiGate or a VDOM to apply security profile features in proxy or flow mode. Change between modes from the System Information dashboard widget. Proxy mode offers the most accurate results and the greatest depth of functionality. Flow mode provides enhanced performance. IPS and application control always operates in flow mode and so is not affected by changing this mode.
Security Profiles > Web Application Firewall
Signatures can now be filtered based on risk level.
The options to reset action and apply traffic shaping is now only available in the CLI.
The All Other Known Applications option has been removed, while the option for All Other Unknown Applications has been renamed Unknown Applications.
Block all Windows executable files (.exe) in email attachments (269781)
A new option has been added to AntiVirus profiles to block all Windows executable files (.exe) in email attachments.
CLI Syntax
config antivirus profile edit “default”
config imap
set executables {default | virus}
end
config pop3
set executables {default | virus}
end config smtp
set executables {default | virus}
end
config mapi
set executables {default | virus}
end end
end
Cookies can now be used to authenticate users when a web filter override is used (275273)
Cookies can be used to authenticate users when a web filter override is used. This feature is available in CLI only.
CLI Syntax
config webfilter cookie-ovrd set redir-host <name or IP> set redir-port <port>
end
config webfilter profile edit <name>
config override
set ovrd-cookie {allow | deny}
set ovrd-scope {user | user-group | ip | ask}
set profile-type {list | radius} set ovrd-dur-mode {constant | ask} set ovrd-dur <duration>
set ovrd-user-group <name>
set profile <name>
end end
end
Blocking malicious URLs (277363)
A local malicious URL database dowloaded from FortiGuard has been added to assist IPS detection for live exploits, such as drive-by attacks. You enable blocking malicious URLs in an IPS profile from the CLI using the following command:
CLI Syntax
config ips sensor edit default
set block-malicious-url {enable | disable}
next end
The FortiGuard IPS/AV update schedule can be set by time intervals (278772)
This feature allows updates to occur more frequently (syntax below shown for updates randomly every 2-3 hours).
CLI Syntax
config system autoupdate schedule set frequency every set time 02:60 end
Application Control signatures belonging to industrial category/group are excluded by default (277668)
Use the following command to be able to add industrial signatures to an application control sensor:
config ips global
set exclude-signatures {none | industrial}
end
The Indistrial category now appears on the Application Control sensor GUI.
An SSL server table can now be used for SSL offloading (275273)
CLI Syntax
config firewall ssl-ssh-profile edit <name>
set use-ssl-server {enable | disable}
next end
MAPI RPC over HTTP/HTTPS traffic is now supported for security scanning (278012)
CLI Syntax
config firewall profile-protocol-options edit “default”
set comment “All default services.” config http
set ports 80 3128
set options rpc-over-http end
end end
New Dynamic DNS FortiGuard web filtering sub-category (276495)
A new FortiGuard web filtering sub-category, Dynamic DNS, has been added and can be found in the Security Risk Category. Also, the sub-category Shopping and Auction has been separated into two sub-categories: Auction and Shopping.
New Filter Overrides in the Application Sensor GUI (260901)
The overrides allow you to select groups of applications and override the application signature settings for them.
FortiGate CA certificates installed on managed FortiClients (260902)
This feature allows you to enable or disable CA certificate installation on managed FortiClients in a FortiClient Profile.
Syntax
config endpoint-control profile edit <profile>
config forticlient-winmac-settings
set install-ca-certificate [enable | disable]
end next
end
More exemptions to SSL deep inspection (267241)
Some common sense exemptions have been added to the default SSL deep inspection profile, such as Fortinet, Android, Apple, Skype, and many more.
Exempting URLs for flow-based web filtering (252010)
You can once again exempt URLs for flow-based web filtering.
Filter overrides in Application Sensors (246546)
In the Application Sensor page, a new section named Filter Overrides has been introduced. From this section, clicking Add Filter/Edit Filter will launch a dialog to pick/edit the advanced filter and save it back to the list.
New keyword byte_extract for custom IPS and Application Control signatures (179116)
The new byte_extract custom IPS signature key has been added that supports snort-like byte extraction actions. It is used for writing rules against length-encoded protocols. The keyword reads some of the bytes from the packet payload and saves it to a variable. You can use the -quiet option to suppress the reporting of signatures.
IPS logging changes (254954)
IPS operations severely affected by disk logging are moved out of the quick scanning path, including logging, SNMP trap generation, quarantine, etc.
Scanning processes are dedicated to nothing but scanning, which results in more evenly distributed CPU usage. Slow (IPS) operations are taken care of in a dedicated process, which usually stays idle.
New FortiGuard web filtering category: Dynamic DNS (265680)
A new FortiGuard web filtering category has been added forDynamic DNSunder theSecurity Riskheading, to account for nearly half a million URLs of “Information Technology” rated by BlueCoat as “Dynamic DNS Host”.
Syntax
config webfilter profile edit <profile>
config ftgd-wf config filters
edit <id>
set category 88<— New category, Dynamic DNS; number 88
end end
end
Access Control Lists in DoS Policies (293399)
You can go to Policy & Objects > IPv4 Access Control List or Policy & Objects > IPv6 Access Control List and select an incoming interface and add a list of Firewall source and destination addresses and services and drop traffic that matches.
You can use the following CLI command to add an ACL:
config firewall acl edit 1
set interface “port1”
set srcaddr “google-drive” set dstaddr “all”
set service “ALL” next
end
WebSense web filtering through WISP (287757)
WISP is a Websense protocol that is similar in functionality to ICAP, it allows for URLs to be extracted by a firewall and submitted to WebSense systems for rating and approval checking.
This feature provides a solution for customers who have large, existing, deployed implementations of Websense security products to replace their legacy firewalls with a Fortigate family, such that they are not forced to make a change to their web filtering infrastructure at the same time.
In order to use WebSense’s web filtering service, a WISP server per VDOM needs to be defined and enabled first. A Web filtering profile is then defined that enables WISP, which in turn is applied to a firewall policy.
When WISP is enabled, the FortiGate will maintain a pool of TCP connections to the WISP server. The TCP connections will be used to forward HTTP request information and log information to the WISP server and receive policy decisions.
Syntax
config web-proxy wisp set status enable
set server-ip 72.214.27.138 set max-connection 128
end
config webfilter profile edit “wisp_only”
set wisp enable next
end
Other new Security Profiles features:
- CPU allocation & tuning commands now remain after a system reboot (276190)
- The GUI notifies an administrator when the FortiGate is in conserve mode (266937)
- A new custom IPS signature option, “–ip_dscp” has been added to be compatible with engine 1.x. (269063 )
- The RTP/RTSP decoder can now detect slave sessions (273910)
- ISNIFF can now dump all HTML files if the dump-all-html CLI command is used (277793)
- Sender and recipient fields have been added to flow-based SMTP spam logs (269063)
- Browser Signature Detection added to Application Control profiles (279934)