L2TP and IPsec (Microsoft VPN)
This section describes how to set up a VPN that is compatible with the Microsoft Windows native VPN, which is
Layer 2 Tunneling Protocol (L2TP) with IPsec encryption. The following topics are included in this section:
- Overview
- Assumptions
- Configuring the FortiGate unit Configuring the Windows PC Troubleshooting
Overview
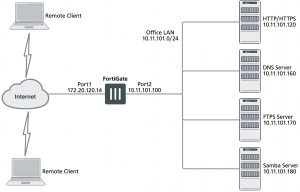
The topology of a VPN for Microsoft Windows dialup clients is very similar to the topology for FortiClient Endpoint Security clients.
Example FortiGate VPN configuration with Microsoft clients
For users, the difference is that instead of installing and using the FortiClient application, they configure a network connection using the software built into the Microsoft Windows operating system. Starting in FortiOS 4.0
MR2, you can configure a FortiGate unit to work with unmodified Microsoft VPN client software.
Layer 2 Tunneling Protocol (L2TP)
L2TP is a tunneling protocol published in 1999 that is used with VPNs, as the name suggests. Microsoft Windows operating system has a built-in L2TP client starting since Windows 2000. Mac OS X 10.3 system and higher also have a built-in client.
L2TP provides no encryption and used UDP port 1701. IPsec is used to secure L2TP packets. The initiator of the L2TP tunnel is called the L2TP Access Concentrator (LAC).
L2TP and IPsec is supported for native Windows XP, Windows Vista and Mac OSX native VPN clients. However, in Mac OSX (OSX 10.6.3, including patch releases) the L2TP feature does not work properly on the Mac OS side.
Assumptions
The following assumptions have been made for this example:
- L2TP protocol traffic is allowed through network firewalls (TCP and UDP port 1701)
- User has Microsoft Windows 2000 or higher — a Windows version that supports L2TP
Configuring the FortiGate unit
To configure the FortiGate unit, you must:
- Configure LT2P users and firewall user group.
- Configure the L2TP VPN, including the IP address range it assigns to clients.
- Configure an IPsec VPN with encryption and authentication settings that match the Microsoft VPN client.
- Configure security policies.
Configuring LT2P users and firewall user group
Remote users must be authenticated before they can request services and/or access network resources through the VPN. The authentication process can use a password defined on the FortiGate unit or an established external authentication mechanism such as RADIUS or LDAP.
Creating user accounts
You need to create user accounts and then add these users to a firewall user group to be used for L2TP authentication. The Microsoft VPN client can automatically send the user’s Window network logon credentials. You might want to use these for their L2TP user name and password.
To create a user account – web-based manager
1. Go to User & Device > User Definition and select Create New.
2. Enter the User Name.
3. Do one of the following:
- Select Password and enter the user’s assigned password.
- Select Match user on LDAP server, Match user on RADIUS server, or Match user onTACACS+ server and select the authentication server from the list. The authentication server must be already configured on the FortiGate unit.
4. Select OK.
To create a user account – CLI
To create a user account called user1 with the password 123_user, enter:
config user local edit user1
set type password
set passwd “123_user” set status enable
end
Creating a user group
When clients connect using the L2TP-over-IPsec VPN, the FortiGate unit checks their credentials against the user group you specify for L2TP authentication. You need to create a firewall user group to use for this purpose.
To create a user group – web-based manager
1. Go to User & Device > User Groups, select Create New, and enter the following:
Name Type or edit the user group name (for example, L2TP_group).
Type Select Firewall.
Available Users/Groups The list of Local users, RADIUS servers, LDAP servers, TACACS+ servers, or PKI users that can be added to the user group. To add a member to this list, select the name and then select the right arrow button.
Members The list of Local users, RADIUS servers, LDAP servers, TACACS+ servers, or PKI users that belong to the user group. To remove a member, select the name and then select the left arrow button.
2. Select OK.
To create a user group – CLI
To create the user group L2TP_group and add members User_1, User_2, and User_3, enter:
config user group edit L2TP_group
set group-type firewall
set member User_1 User_2 User_3 end
Configuring L2TP
You can only configure L2TP settings in the CLI. As well as enabling L2TP, you set the range of IP address values that are assigned to L2TP clients and specify the user group that can access the VPN. For example, to allow access to users in the L2TP_group and assign them addresses in the range 192.168.0.50 to 192.168.0.59, enter:
config vpn l2tp
set sip 192.168.0.50 set eip 192.168.0.59 set status enable
set usrgrp “L2TP_group” end
One of the security policies for the L2TP over IPsec VPN uses the client address range, so you need also need to create a firewall address for that range. For example,
config firewall address edit L2TPclients
set type iprange
set start-ip 192.168.0.50 set end-ip 192.168.0.59
end
Alternatively, you could define this range in the web-based manager.
Configuring IPsec
The Microsoft VPN client uses IPsec for encryption. The configuration needed on the FortiGate unit is the same as for any other IPsec VPN with the following exceptions.
- Transport mode is used instead of tunnel mode.
- The encryption and authentication proposals must be compatible with the Microsoft client.
Whether Transport mode is required depends on the configuration of the peer device (typically an old Windows device, since newer versions of Windows don’t require IPsec and L2TP—they can run IPsec natively).
When configuring L2TP, do not name the VPN “L2TP” as that will result in a conflict.
L2TP over IPsec is supported on the FortiGate unit for both policy-based and route-based configurations, but the following example is policy-based.
Configuring Phase 1 – web-based manager
1. Go to VPN > IPsec Tunnels and create the new custom tunnel or edit an existing tunnel.
2. Edit the Phase 1 Proposal (if it is not available, you may need to click the Convert to Custom Tunnel button).
Name Enter a name for this VPN, dialup_p1 for example.
Remote Gateway Dialup User
Local Interface Select the network interface that connects to the Internet. For example, port1.
Mode Main (ID protection)
Authentication Method Preshared Key
Pre–shared Key Enter the preshared key. This key must also be entered in the Microsoft VPN client.
Advanced Select Advanced to enter the following information.
Phase 1 Proposal Enter the following Encryption/Authentication pairs:
AES256-MD5, 3DES-SHA1, AES192-SHA1
Diffie–Hellman Group 2
NAT Traversal Enable
Dead Peer Detection Enable
Configuring Phase 1 – CLI
To create a Phase 1 configuration called dialup_p1 on a FortiGate unit that has port1 connected to the Internet, you would enter:
config vpn ipsec phase1 edit dialup_p1
set type dynamic
set interface port1 set mode main
set psksecret ********
set proposal aes256-md5 3des-sha1 aes192-sha1 set dhgrp 2
set nattraversal enable
set dpd [disable | on-idle | on-demand]
end
It is worth noting here that the command config vpn ipsec phase1 is used rather than config vpn ipsec phase1-interface because this configuration is policy-based and not route-based.
Configuring Phase 2 – web-based manager
1. Open the Phase 2 Selectors panel.
2. Enter the following information and then select OK.
Phase 2 Proposal Enter the following Encryption/Authentication pairs:
AES256-MD5, 3DES-SHA1, AES192-SHA1
Enable replay detection Enable
Enable perfect forward secrecy (PFS) Disable
Keylife 3600 seconds
3. Make this a transport-mode VPN. You must use the CLI to do this. If your Phase 2 name is dialup_p2, you would enter:
config vpn ipsec phase2 edit dialup_p2
set encapsulation transport-mode end
Configuring Phase 2 – CLI
To configure a Phase 2 to work with your phase_1 configuration, you would enter:
config vpn ipsec phase2 edit dialup_p2
set phase1name dialup_p1
set proposal aes256-md5 3des-sha1 aes192-sha1 set replay enable
set pfs disable
set keylifeseconds 3600
set encapsulation transport-mode end
Once again, note here that the command config vpn ipsec phase2 is used rather than config vpn ipsec phase2-interface because this configuration is policy-based and not route-based.
Configuring security policies
The security policies required for L2TP over IPsec VPN are:
- An IPsec policy, as you would create for any policy-based IPsec VPN
- A regular ACCEPT policy to allow traffic from the L2TP clients to access the protected network
Configuring the IPsec security policy – web-based manager
1. Go to System > Feature Select and enable Policy-based IPsec VPN.
2. Go to Policy & Objects > IPv4 Policy and select Create New.
3. Set the Action to IPsec and enter the following information:
Incoming Interface Select the interface that connects to the private network behind this
FortiGate unit.
Source Address All
Outgoing Interface Select the FortiGate unit’s public interface.
Destination Address All
VPN Tunnel Select Use Existing and select the name of the Phase 1 configuration that you created. For example, dialup_p1. See Configuring IPsec on page 1781.
Allow traffic to be initiated from the remote site enable
4. Select OK.
Configuring the IPsec security policy – CLI
If your VPN tunnel (Phase 1) is called dialup_p1, your protected network is on port2, and your public interface is port1, you would enter:
config firewall policy edit 0
set srcintf port2 set dstintf port1 set srcaddr all set dstaddr all set action ipsec
set schedule always set service all
set inbound enable
set vpntunnel dialup_p1 end
Configuring the ACCEPT security policy – web-based manager
1. Go to Policy & Objects > IPv4 Policy and select Create New.
2. Leave the Policy Type as Firewall and leave the Policy Subtype as Address.
3. Enter the following information and select OK:
Incoming Interface Select the FortiGate unit’s public interface.
Source Address Select the firewall address that you defined for the L2TP clients.
Outgoing Interface Select the interface that connects to the private network behind this FortiGate unit.
Destination Address All
Action ACCEPT
Configuring the ACCEPT security policy – CLI
If your public interface is port1, your protected network is on port2, and L2TPclients is the address range that L2TP clients use, you would enter:
config firewall policy edit 1
set srcintf port1 set dstintf port2
set srcaddr L2TPclients set dstaddr all
set action accept set schedule always set service all
end
Configuring the Windows PC
Configuration of the Windows PC for a VPN connection to the FortiGate unit consists of the following:
1. In Network Connections, configure a Virtual Private Network connection to the FortiGate unit.
2. Ensure that the IPSEC service is running.
3. Ensure that IPsec has not been disabled for the VPN client. It may have been disabled to make the Microsoft VPN compatible with an earlier version of FortiOS.
The instructions in this section are based on Windows XP. Other versions of Windows may vary slightly.
To configure the network connection
1. Open Network Connections.
This is available through the Control Panel.
2. Double-click New Connection Wizard and Select Next.
3. Select Connect to the network at my workplace.
4. Select Next.
5. Select Virtual Private Network connection and select Next.
6. In the Company Name field, enter a name for the connection and select Next.
7. Select Do not dial the initial connection and then select Next.
8. Enter the public IP address or FQDN of the FortiGate unit and select Next.
9. Optionally, select Add a shortcut to this connection to my desktop.
10. Select Finish.
The Connect dialog opens on the desktop.
11. Select Properties and then select the Security tab.
12. Select IPsec Settings.
13. Select Use pre-shared key for authentication, enter the preshared key that you configured for your VPN, and select OK.
14. Select OK.
To check that the IPSEC service is running
1. Open Administrative Tools through the Control Panel.
2. Double-click Services.
3. Look for IPSEC Services. Confirm that the Startup Type is Automatic and Status is set to Started. If needed, double-click IPSEC Services to change these settings.
To check that IPsec has not been disabled
1. Select Start > Run.
2. Enter regedit and select OK.
3. Find the Registry key HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\RasMan\Parameters
4. If there is a ProhibitIPsec value, it must be set to 0.
Troubleshooting
This section describes some checks and tools you can use to resolve issues with L2TP-over-IPsec VPNs. This section includes:
- Quick checks
- Mac OS X and L2TP
- Setting up logging
- Using the FortiGate unit debug commands
Quick checks
The table below is a list of common L2TP over IPsec VPN problems and the possible solutions.
Problem What to check
IPsec tunnel does not come up.
Check the logs to determine whether the failure is in Phase 1 or Phase 2.
Check the settings, including encapsulation setting, which must be trans- port-mode.
Check the user password.
Confirm that the user is a member of the user group assigned to L2TP. On the Windows PC, check that the IPsec service is running and has not been disabled. See Troubleshooting on page 1786.
Tunnel connects, but there is no communication.
Did you create an ACCEPT security policy from the public network to the protected network for the L2TP clients? See Troubleshooting on page 1786.
Mac OS X and L2TP
FortiOS allows L2TP connections with empty AVP host names and therefore Mac OS X L2TP connections can connect to the FortiGate.
Prior to FortiOS 4.0 MR3, FortiOS refused L2TP connections with empty AVP host names in compliance with RFC 2661 and RFC 3931.
Setting up logging
L2TP logging must be enabled to record L2TP events. Alert email can be configured to report L2TP errors.
To configure FortiGate logging for L2TP over IPsec
1. Go to Log & Report > Log Settings.
2. Select Event Log.
3. Select the VPN activity event check box.
4. Select Apply.
To view FortiGate logs
1. Go to Log & Report > VPN Events.
2. Select the Log location if required.
3. After each attempt to start the L2TP over IPsec VPN, select Refresh to view logged events.
Using the FortiGate unit debug commands
To view debug output for IKE and L2TP
1. Start an SSH or Telnet session to your FortiGate unit.
2. Enter the following CLI commands
diagnose debug application ike -1 diagnose debug application l2tp -1 diagnose debug enable
3. Attempt to use the VPN and note the debug output in the SSH or Telnet session.
4. Enter the following command to reset debug settings to default:
diagnose debug reset
To use the packet sniffer
1. Start an SSH or Telnet session to your FortiGate unit.
2. Enter the following CLI command
diagnose sniffer packet any icmp 4
3. Attempt to use the VPN and note the debug output.
4. Enter Ctrl-C to end sniffer operation.
Typical L2TP over IPsec session startup log entries – raw format
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=ipsec pri=notice vd=”root” msg=”progress IPsec Phase 1″ action=”negotiate” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_ group=”N/A” vpn_tunnel=”dialup_p1″ status=success init=remote mode=main dir=outbound stage=1 role=responder result=OK
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=ipsec pri=notice vd=”root” msg=”progress IPsec Phase 1″ action=”negotiate” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_ group=”N/A” vpn_tunnel=”dialup_p1″ status=success init=remote mode=main dir=outbound stage=2 role=responder result=OK
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=ipsec pri=notice vd=”root” msg=”progress IPsec Phase 1″ action=”negotiate” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_ group=”N/A” vpn_tunnel=”dialup_p1″ status=success init=remote mode=main dir=inbound stage=3 role=responder result=DONE
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=ipsec pri=notice vd=”root” msg=”progress IPsec Phase 1″ action=”negotiate” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_ group=”N/A” vpn_tunnel=”dialup_p1_0″ status=success init=remote mode=main dir=outbound stage=3 role=responder result=DONE
2010-01-11 16:39:58 log_id=0101037129 type=event subtype=ipsec pri=notice vd=”root” msg=”progress IPsec Phase 2″ action=”negotiate” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_group=”N/A” vpn_tunnel=”dialup_p1_0″ status=success init=remote mode=quick dir=outbound stage=1 role=responder result=OK
2010-01-11 16:39:58 log_id=0101037133 type=event subtype=ipsec pri=notice vd=”root” msg=”install IPsec SA” action=”install_sa” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_ group=”N/A” vpn_tunnel=”dialup_p1_0″ role=responder in_spi=61100fe2 out_spi=bd70fca1
2010-01-11 16:39:58 log_id=0101037139 type=event subtype=ipsec pri=notice vd=”root” msg=”IPsec Phase 2 status change” action=”phase2-up” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_group=”N/A” vpn_tunnel=”dialup_p1_0″ phase2_name=dialup_p2
2010-01-11 16:39:58 log_id=0101037138 type=event subtype=ipsec pri=notice vd=”root” msg=”IPsec connection status change” action=”tunnel-up” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_ user=”N/A” xauth_group=”N/A” vpn_tunnel=”dialup_p1_0″ tunnel_ip=172.20.120.151 tunnel_id=1552003005 tunnel_type=ipsec duration=0 sent=0 rcvd=0 next_stat=0 tunnel=dialup_p1_0
2010-01-11 16:39:58 log_id=0101037129 type=event subtype=ipsec pri=notice vd=”root” msg=”progress IPsec Phase 2″ action=”negotiate” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_ group=”N/A” vpn_tunnel=”dialup_p1_0″ status=success init=remote mode=quick dir=inbound stage=2 role=responder result=DONE
2010-01-11 16:39:58 log_id=0101037122 type=event subtype=ipsec pri=notice vd=”root” msg=”negotiate IPsec Phase 2″ action=”negotiate” rem_ip=172.20.120.151 loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_ intf=”port1″ cookies=”5f6da1c0e4bbf680/d6a1009eb1dde780″ user=”N/A” group=”N/A” xauth_user=”N/A” xauth_ group=”N/A” vpn_tunnel=”dialup_p1_0″ status=success role=responder esp_transform=ESP_3DES esp_auth=HMAC_ SHA1
2010-01-11 16:39:58 log_id=0103031008 type=event subtype=ppp vd=root pri=information action=connect status=success msg=”Client 172.20.120.151 control connection started (id 805), assigned ip 192.168.0.50″ 2010-01-11 16:39:58 log_id=0103029013 type=event subtype=ppp vd=root pri=notice pppd is started
2010-01-11 16:39:58 log_id=0103029002 type=event subtype=ppp vd=root pri=notice user=”user1″ local=172.20.120.141 remote=172.20.120.151 assigned=192.168.0.50 action=auth_success msg=”User ‘user1’ using l2tp with authentication protocol MSCHAP_V2, succeeded”
2010-01-11 16:39:58 log_id=0103031101 type=event subtype=ppp vd=root pri=information action=tunnel-up tunnel_id=1645784497 tunnel_type=l2tp remote_ip=172.20.120.151 tunnel_ip=192.168.0.50 user=”user1″ group=”L2TPusers” msg=”L2TP tunnel established”

I setup a L2TP vpn per this doc and it works as far as browsing network shares from the client. The internet however doesn’t work unless I disable Use Default Gateway on remote network on the client side. I’d like to pass all traffic including internet across the VPN. Any ideas?
Do you have a policy allowing the interface the L2TP comes over OUT to the WAN (internet) interface?
That was my issue. I created a WAN to WAN rule for the L2TP range and now internet passes just fine.
Thanks!
Awesome!
Do you create a rule From Wan1 To Wan1?
No, You create interfaces and assign them to the various items (like IPSec interfaces are for IPSec tunnels etc) From there you make policies from the source interface / address space to the destination interface / address space. So if you are receiving traffic from an IPSec tunnel etc to the LAN interface your policy would say IPSEC_INTERFACE_NAME to LAN allow this. Etc
Hi Mike,
very nice article, we are having strange issue. i have route based IPSec vpn, we can only connection 10-13 user using windows build-in client. After that we get error 809 stating you network device could be behind NAT, Firewall. not sure what we are doing wrong but could not fine solution. Any help would be appreciated.
Kind Regards